What is the TRACED Act, and How Does it Impact Emergency Communications?
A comprehensive guide that explores the governing bodies, legislation, and technical terminology that defines this complex issue
The TRACED Act aims to protect residents from disruptive, unwanted, fraudulent, and potentially harmful solicitations by marketers and nefarious spammers by phone or text. It also might inadvertently interfere with how public safety leaders issue vital news and information to subscribed residentsor residents or travelers in the path of an emergency. The comprehensive guide that follows explores the governing bodies, legislation, and technical terminology that defines this complex issue and helps public safety leaders understand its short and long-term implications for resident emergency communications.
What is an Automatic Telephone Dialing System (ATDS)
The TCPA defines an ATDS as equipment that has the capacity to:
- Store or produce telephone numbers to be called, using a random or sequential number generator; and
- To dial such numbers
What is a Robocall?
A robocall is a phone call that uses a computerized ATDS to deliver a prerecorded message, often sounding as if the voice speaking is coming from a robot. Robocalls are commonly used to share marketing or political campaign messages; however, the use of auto-dialing to deliver a computerized message is also used by subscription-based emergency notification systems, such as the CivicPlus® Mass Notification System.
What is a Spoof Call?

A spoofed call is one in which a scammer masks their identity by changing the number that is displayed on a caller ID using advanced technology.
What is the TCPA?
The Telephone Consumer Protection Act of 1991 amended the Communications Act of 1934. It restricts telephone solicitations or telemarketing, the use of automated telephone equipment, and limits the use of automatic dialing systems, artificial or prerecorded voice messages, SMS text messages, and fax machines for marketing purposes. The TCPA is the legislative precursor to the TRACED Act.
What is the TRACED Act?
President Trump signed the Pallone-Thune Telephone Robocall Abuse Criminal Enforcement and Deterrence (TRACED) Act into law on December 30, 2019. It gives the Federal Communications Commission (FCC) and law enforcement greater authority to prosecute telephone call scammers, and it should make it easier for residents to identify robocalls and avoid answering them.
The TRACED Act requires telecommunications service providers, such as Verizon, T-Mobile/Sprint, and AT&T, to implement a number-authentication system at no cost to consumers, to help network subscribers identify callers. It also increases penalties for robocallers that continue to solicit residents by phone.
The FCC can now levy civil penalties of up to $10,000 per call on unsolicited telemarketing attempts. The TRACED Act also gives law enforcement more time to go after robocallers by extending the statute of limitations to four years.
The TRACED Act comes in response to residents feeling overwhelmed and fed up with the number of telemarketing calls they receive. In 2018, Americans received a total of 48 billion robocalls, and as of November 2019, that number had skyrocketed to 54 billion according to Consumer Reports. As a result of such abuse, 70 percent of Consumer Reports survey respondents reported that they do not answer the phone if they do not recognize the caller to avoid speaking with a telemarketer. Now, the TRACED Act should mitigate the number of robocalls, and help residents more easily identify and ignore them.
The TRACED Act also intends to combat spoofed calls by requiring the use of the STIR/SHAKEN Authentication System.
What is the STIR/SHAKEN Authentication Framework?

The Secure Telephone Identity Revisited (STIR) and Signature-based Handling of Asserted Information Using toKENs (SHAKEN) is a framework of interconnected standards. Since some marketers have learned to thwart caller identification systems by using spoofed numbers, the STIR/SHAKEN authentication system uses digital fingerprints, or tokens to help determine whether the number from which a call is placed is the same as the number that shows up on a caller ID screen. STIR/SHAKEN digital fingerprints enable carriers to quickly scan their networks to identify, investigate, and block spoofed numbers—a process that used to take months or years of manual investigation.
Many telecommunications carriers have already implemented STIR/SHAKEN technology, which allows residents to receive a warning on incoming phone calls that says “Spam Risk” or “Spam Likely.” Smaller carriers, however, particularly those within the Rural Broadband Association (NTCA) still use older analog technology and need time to implement the use of digital fingerprints. They are not exempt from the TRACED Act requirements, however, and must still implement robocall mitigation programs.
Defining Consumer Consent
One point of clarification needed that the TRACED Act currently lacks is what constitutes consumer consent to receive marketing calls. Consumer advocates argue that without clear guidance as to how a resident can give or withdraw their consent from a source, robocallers may find loopholes and continue to issue undesired calls. This unclear element of the legislation also poses concerns for public safety departments that utilize mass notification systems like CivicPlus to deliver subscription-based emergency alerts to residents during a local disaster.
Additional Potential Loopholes
Another possible loophole within the TRACED Act and current applicable technology come from international robocalls that can skirt U.S.-based authentication standards and law enforcement. This gap gives marketers and scammers the ability to continue robot dialing from international virtual call centers.
Extending the TRACED Act to RoboTexts and Smishing
Voice calls are not the only form of bothersome unsolicited digital marketing plaguing communication device owners. The TRACED Act also allows the FCC to create rules to protect residents from receiving unwanted robotexts and smishing attempts when a scammer issues a phishing attack (sending a message that appears to come from a known contact) via text message. As with email phishing attacks, scammers masquerade as tech support representatives, government workers, friends, family, or financial institutions and attempt to coax residents into providing personally identifiable information such as bank account numbers, credit card numbers, or social security numbers that might lead to fraudulent purchases or identity theft.
What Does the TRACED Act Mean for Entities that Use Legitimate Call Masking?
The TCPA’s restriction on using an automatic telephone dialing system or an artificial or prerecorded voice does not apply to calls made for an “emergency purpose,” defined as calls made necessary in any situation affecting the health and safety of consumers. However, public safety alerts might inadvertently be halted by the STIR/SHAKEN system.
For businesses and public safety departments that use call masking technology to issue business correspondence or emergency alerts, the TRACED Act is creating complications. For example, when a public safety office issues an emergency alert via its mass notification system, it is not coming directly from the public safety director’s desk but rather from a dedicated masked number. Under the legislation, legitimate service providers may continue using masked numbers but must register them in a way that will not trigger an inadvertent flagging by STIR/SHAKEN systems.
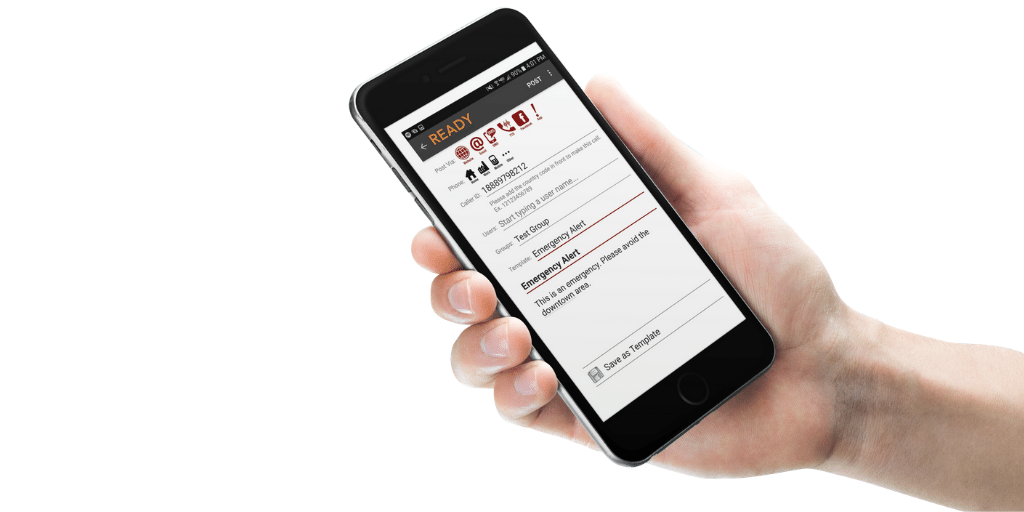
For CivicPlus Mass Notification system’s administrative users, our technical support team can set up a custom reverse call-back number to help comply with TRACED Act regulations and minimize STIR/SHAKEN system interference.
For more information about complying with the TRACED Act, refer to FEMA’s Effective Communication training guide.
TCPA’s Emergency Purpose Exception and the COVID-19 Pandemic
Understanding that residents need immediate updates, news, and information from trusted sources such as hospitals, health care agencies, and municipalities during the COVID-19 crisis, On March 20, 2020, the FCC issued a sua sponte Declaratory Ruling narrowing the TCPA’s emergency purpose exception in the context of calls “relating to the COVID-19 pandemic.” The Declaratory Ruling confirms that the COVID-19 pandemic constitutes an imminent health risk to the public and that “[a] critical component of the nation’s efforts to address and contain this health-related emergency is the ability of health care and public safety organizations to communicate effectively with the public.”
Within these guidelines, a robocall will be permitted as an emergency notification as long as:
- The caller is a hospital, health care provider, state or local health official, or another government official as well as a person under the express direction of such an organization and acting on its behalf
- The content of the call is solely informational, made necessary because of the COVID-19 outbreak, and directly related to the imminent health or safety risk arising out of the COVID-19 outbreak.
For more information, refer to the FCC’s ruling regarding utility notifications, TCPA, and COVID-19.
What is the FCC’s Timeline for Enforcement?
The FCC must complete several actions between the time of the TRACED Act’s signing and the end of 2022. The following FCC compliance timeline was reported by The National Law Review on January 6, 2020.
By June 27, 2020
- The FCC must begin a new proceeding to determine how the FCC could modify its policies to reduce access to numbers by potential robocall law violators.
By July 27, 2020
- The FCC must issue a Public Notice seeking information from voice service providers and the Registered Consortium on voice service providers’ participation in the private-led efforts to trace back the origin of suspected unlawful robocalls and on recommendations to the FCC regarding how it can use the information provided by the Registered Consortium in its enforcement efforts.
By September 25, 2020
- The FCC must adopt and issue regulations to implement the amendments to Section 227 made by the TRACED Act.
- In conjunction with the interagency working group convened under this Act, the FCC must submit to the Committees of jurisdiction in the House and the Senate a report on the findings of the required studies regarding TCPA violations.
By December 30, 2020
- The FCC must submit to Congress:
- After consulting with the Federal Trade Commission (FTC), the FCC is to present a report on enforcement actions taken against unlawful robocalls and spoofed calls during the preceding calendar year, which must be due to Congress annually.
- A report on the status of the FCC’s efforts to establish the Recycled Number Database, which must be available on the FCC’s website.
- The FCC must submit to the Committee on Energy and Commerce of the House of Representatives and the Committee on Commerce, Science, and Transportation of the Senate:
- A report of its determinations about the status of adoption of STIR/SHAKEN authentication framework by voice service providers in IP networks and the status of implementing an effective call authentication framework by voice service providers in non-IP networks;
- A report that states the number of instances during 2020 that the FCC provided evidence of willful, knowing, and repeated robocall violation to the Attorney General, as well as a summary of the types of robocall violations that were proved. This report also is to be available on the FCC’s website. This report is due to the Congressional Committees annually going forward.
- A report on the status of the proceedings the FCC initiated to protect called parties from one-ring scams. This report must also be published on the FCC’s website.
- A report on the status of private industry-led efforts to trace back the origin of suspected unlawful robocalls by the Registered Consortium and the participation of voice service providers in such efforts. This report must also be published on the FCC’s website. This report is due annually to the Committees on December 30.
- The FCC must conduct an assessment on any material new burdens or legal or practical barriers to the implementation of the required call authentication frameworks and, upon a public finding of undue hardship, the FCC may delay required compliance for a “reasonable” period of time to be specified by the FCC.
- The FCC must issue best practices that voice service providers may use as part of the implementation of effective call authentication framework to ensure that the calling party is accurately identified.
- The FCC also must issue rules that address:
- When a voice service provider may block a voice call based, in whole or in part, on information provided by the required call authentication frameworks with no additional line item charge;
- A safe harbor for voice service providers from liability for unintended or inadvertent blocking of calls or for the unintended or inadvertent misidentification of the level of trust for individual calls based, in whole or in part, on information provided by the required call authentication frameworks;
- A process to permit a calling party adversely affected by the information provided by the required call authentication frameworks to verify the authenticity of the calling party’s calls; and
- Ensuring that calls originating from a voice service provider in an area where the provider is subject to a delay of compliance authorized by the FCC are not unreasonably blocked because the calls are not able to be authenticated.
- The FCC must begin a rulemaking proceeding to protect subscribers from receiving unwanted calls or text messages from callers using unauthenticated numbers.
- The FCC must issue new regulations or amend existing regulations related to exemptions under the TCPA so that such exemption must specify the classes of parties that may make calls or texts, the classes of parties that may be called, and the number of calls that a calling party may make to a particular called party.
- The FCC must take a final agency action to ensure that the robocall blocking services provided under the “Call Blocking by Default” regime are provided with transparency and effective redress options, with no additional line charge, and reasonable efforts are made to avoid blocking emergency public safety calls.
By June 30, 2021
- The FCC must require voice service providers to implement the STIR/SHAKEN authentication framework on all IP networks and to take reasonable measures to implement an effective call authentication framework on all non-IP networks.
- The FCC must issue regulations establishing a process to streamline the ways in which a private entity may voluntarily share information with the FCC about calls made or text messages sent for which misleading or inaccurate caller ID information was transmitted in violation of the TCPA’s prohibition against unlawful spoofed calls.
- The FCC must submit to Congress a report on the results of a study addressing whether certain VoIP service providers should be required to maintain contact information on file with the FCC and retain records relating to each call transmitted over the VoIP service that would be sufficient to trace such a call or text back to its source.
December 30, 2022
- After having issued a Public Notice and sought public comments, the FCC is to issue a report on the efficacy of the technologies used for call authentication frameworks. The FCC must also determine whether the required call authentication framework needs to be revised or replaced, and then compile this information along with any proposed actions and submit this report to the Congressional Committees of jurisdiction. The review, determination, and report are also required every three years beyond the year of 2022.
Note: Information in this article does not constitute legal advice.


